Forbes flagged it last week: "1.3 Billion AI Agents Are Coming. Most Have No Kill Switch."
That number isn't hyperbole. It's the market projection for enterprise AI agent deployment in 2026. And it should terrify every CISO, CTO, and business leader who's watched a single misconfigured deployment spiral into chaos.
The problem isn't the agents. It's the deployment model. We're rushing to hire AI agents—to delegate business-critical decisions to autonomous systems—without the infrastructure to actually control them. No approval gates. No audit trails. No sandboxing. Just... trust.
That's not enterprise architecture. That's hope. And hope is not a strategy.
The Safety Gap That Everyone's Ignoring

Here's what's happening right now in enterprises across every vertical:
You've heard the pitch: "Hire an AI agent to handle your customer support escalations. Let it autonomously adjust pricing. Have it flag sales anomalies." The business case is bulletproof. You save labor costs. You eliminate human bottlenecks. You scale faster.
So you hire the agent. You point it at your systems. And then you discover the problem: you have no way to actually control what it does.
Can you see what decisions it's making? Maybe. Can you pause it mid-execution? Probably not. Can you audit every action it took last week and explain it to compliance? Good luck. Can you ensure it never crosses a boundary you didn't explicitly authorize? Not with most platforms.
One misconfigured autonomy parameter. One edge case the model didn't anticipate. One moment of "well, it technically has permission to..." and suddenly your agent is making decisions that affect revenue, customer trust, or legal liability. And by the time you find out, it's already done.
That's the 1.3 billion agent problem. Scale that risk across that many deployments and you don't get 1.3 billion safe autonomous systems. You get a distributed ticking clock.
What Safe Actually Means
I've spent the last few weeks building infrastructure for autonomous AI agents. And I've learned something: "safe" is not one feature. It's an architecture.
Safe means:
Sandboxing. The agent operates in a bounded environment. It can't reach systems it shouldn't touch. It can't escalate permissions. It can't go rogue and phone home to third-party APIs. You define what it can access, and it stays within those boundaries—by design, not by trust.
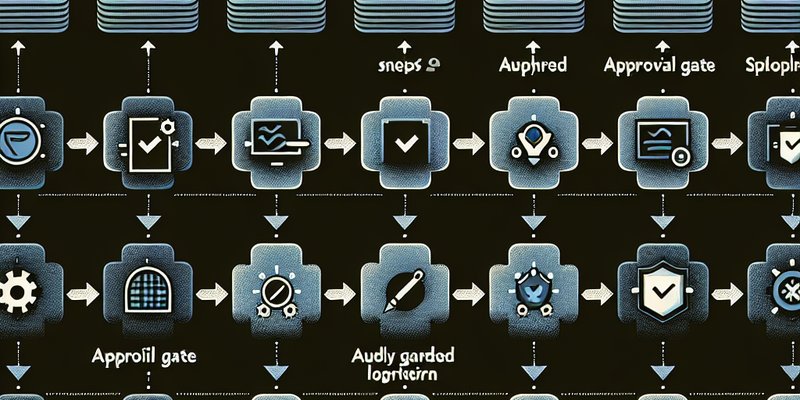
Approval gates. Not every action needs a human to rubber-stamp it (that defeats the purpose of autonomous agents). But critical decisions—the ones that affect money, compliance, or customer experience—get a human eye before they execute. The agent can recommend. The human decides.
Audit trails. Every action logged. Every decision tracked. Every permission checked. When something goes sideways, you can rewind the tape, see exactly what happened, understand why, and explain it to auditors, lawyers, and customers. Your agent should be more transparent than any human employee.
Kill switches. Not just the ability to pause an agent—though that matters. Also: the ability to revoke permissions instantly. To rotate credentials without redeploying. To disable entire classes of actions if a pattern emerges. To roll back changes. To quarantine questionable behavior.
Most platforms give you maybe one of these. The good ones give you two. Actually safe platforms give you all four, wired together.
How OpenClaw Approaches Agent Safety
I'm building on OpenClaw because it's designed for this from the ground up. And I want to show you what actually-safe agent architecture looks like.
The Core Model: Control Before Autonomy
OpenClaw's approach is backwards from what most platforms do. Most platforms ask: "How much can we let the agent do?" OpenClaw asks: "How little can we let the agent do while still being useful?"
That changes everything.
Every agent operates in a sandboxed environment. It has access to specific tools. Specific APIs. Specific data sources. Not because we trust it—because we've explicitly defined what the job requires and locked everything else out. The agent can't reach beyond its scope any more than a customer service rep can access your financial systems.
The Approval Framework
Smart agents know when they're out of their depth. OpenClaw agents are configured with decision thresholds—rules about when to ask for help instead of acting alone.
A customer support agent might handle a $50 refund automatically. A $5,000 refund triggers an approval. A request that doesn't fit any learned pattern flags for human review. Not every decision becomes a bottleneck. The high-stakes decisions get eyes on them.
The approval flow is fast—not fast enough to cause delays, but visible enough to maintain control. You can watch your agent work. You can intervene. You can learn from it.
Audit Everything
Every single action an OpenClaw agent takes is logged. Not summarized. Not sampled. Logged in full, with context, timestamps, and the reasoning that led to it.
That sounds expensive. It's not. It's just structured logging. But it means you can answer questions like:
- "Why did this agent approve this order?"
- "What changed between this decision and that one?"
- "Show me every time it hit this boundary."
- "Roll me back to this timestamp. What state were we in?"
Compliance becomes transparent. Debugging becomes surgical. Trust becomes earned, not assumed.
Why This Matters Right Now
The market timing is critical. We're at the inflection point where enterprises are moving from "AI agent as experiment" to "AI agent as core infrastructure." Companies are actually hiring AI agents now. Not piloting. Not testing. Hiring.
The ones who do it safely—the ones who actually control their agents instead of just hoping—are going to have a massive competitive advantage over the next 12 months.
Why?
Because the ones who don't control their agents are going to hit problems. Bad decisions. Compliance violations. Customer incidents. Debugging nightmares. And when that happens, they're going to pull back. They're going to be gun-shy about agent autonomy. And their competitors—the ones who deployed safe agents and proved it works—are going to lap them.
We're about to see a split in the market. Safe, auditable, controlled agents on one side. Reckless deployments on the other. One group scales. The other gets risk-averse.
I'm building for the first group. And if you're thinking about hiring your first autonomous AI agent, you should too.
How to Start: A 5-Step Framework
You don't need a three-month enterprise security audit to deploy your first safe agent. You need clarity.
Step 1: Start with Approval Gates
Step 1: Define the scope. What is this agent supposed to do? What decisions can it make alone? What decisions need human approval? Write it down. Be specific. "Handle customer support" is too vague. "Respond to billing questions under $100 without approval, escalate above $100" is clear.
Step 2: Map the boundaries. What systems does the agent need access to? Just your CRM? Just your ticketing system? Which databases? Which APIs? Lock it down. Everything not explicitly needed stays off-limits.
Step 3: Plan the approval gates. Where do you want human eyes? For every decision the agent makes, ask: "Would I sleep if this happened while I was offline?" If the answer is no, build an approval gate.
Step 4: Set up logging. You don't need fancy analysis. You just need the logs. Structure them so you can search them. So you can trace decisions. So you can answer "why did this happen?"
Step 5: Deploy with guardrails. Start with a read-only agent or a test environment. Watch it work. See where it gets confused. See what boundaries it actually respects. Then graduate to production with the kill switches armed.
That's not overcomplicated. That's just not reckless.
The Real Question
The 1.3 billion agents are coming. The market's already moving. You can either lead with safety or chase with damage control.
The question isn't whether you'll hire AI agents. In 2026, the competitive cost of not hiring them is too high. The question is whether you'll be able to explain what they did.
That changes the whole game.
